160 CrackMe 是比较适合新手学习逆向破解的CrackMe的一个集合一共160个待逆向破解的程序
CrackMe:它们都是一些公开给别人尝试破解的小程序,制作 crackme 的人可能是程序员,想测试一下自己的软件保护技术,也可能是一位 cracker,想挑战一下其它 cracker 的破解实力,也可能是一些正在学习破解的人,自己编一些小程序给自己破。
来源 <-点击查看
| 编号 | 作者 | 保护方式 |
| 030 | cracking4all | Serial(VB5) |
工具
x32dbg
VB Decompiler Pro
开始破解之旅 ON.1爆破方式
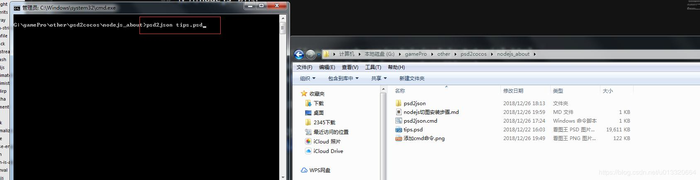
使用x32dbg打开031号程序&#xff0c;右键搜索字符串

此时我们看见了正确提示字符提示信息和错误字符提示信息&#xff0c;进入正确提示信息地址为00403005&#xff0c;双击进入该地址&#xff0c;向上翻看
00402FAE | C785 28FFFFFF 08800000 | mov dword ptr ss:[ebp-D8],8008 |
00402FB8 | FF15 4C614000 | call dword ptr ds:[<&__vbaVarTstEq>] |
00402FBE | 66:85C0 | test ax,ax |
00402FC1 | 0F84 8F000000 | je cracking4all.2.403056 | 此处跳转&#xff0c;为验证输入密码
00402FC7 | B8 04000280 | mov eax,80020004 |
00402FCC | 8D95 18FFFFFF | lea edx,dword ptr ss:[ebp-E8] | edx:EntryPoint
00402FD2 | 8D4D 88 | lea ecx,dword ptr ss:[ebp-78] |
00402FD5 | 8985 70FFFFFF | mov dword ptr ss:[ebp-90],eax |
00402FDB | 899D 68FFFFFF | mov dword ptr ss:[ebp-98],ebx |
00402FE1 | 8945 80 | mov dword ptr ss:[ebp-80],eax |
00402FE4 | 899D 78FFFFFF | mov dword ptr ss:[ebp-88],ebx |
00402FEA | C785 20FFFFFF 68264000 | mov dword ptr ss:[ebp-E0],cracking4all. | 402668:L"Valid"
00402FF4 | 89BD 18FFFFFF | mov dword ptr ss:[ebp-E8],edi |
00402FFA | FFD6 | call esi |
00402FFC | 8D95 28FFFFFF | lea edx,dword ptr ss:[ebp-D8] | edx:EntryPoint
00403002 | 8D4D 98 | lea ecx,dword ptr ss:[ebp-68] |
00403005 | C785 30FFFFFF 2C264000 | mov dword ptr ss:[ebp-D0],cracking4all. | 40262C:L"Password correct, hehe, :-)"
0040300F | 89BD 28FFFFFF | mov dword ptr ss:[ebp-D8],edi |
此时我们看到00402FC1处有一处跳转&#xff0c;在上方00402FB8处调用匹配函数&#xff0c;验证是否相等&#xff0c;此处跳转为密码验证跳转&#xff0c;将其修改为NOP我们测试一下

bingo ~ 破解成功
ON.2追码方式
使用VB Decompiler Pro打开031号程序&#xff0c;我们在左侧选中Code -> password -> Command1_Click&#xff0c;右侧及显示反汇编的代码
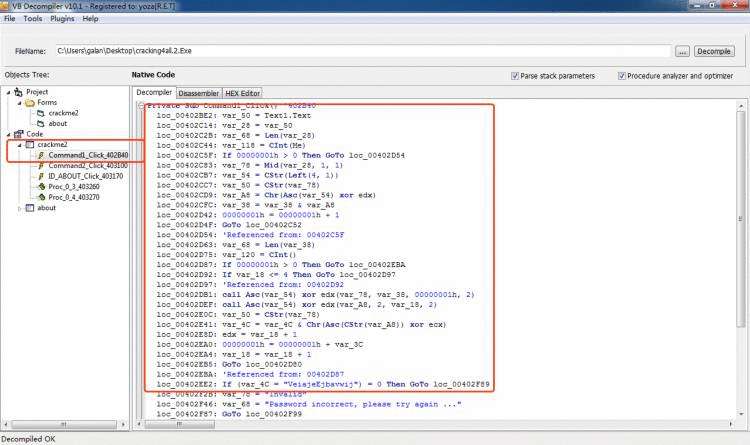
我们可以看出该函数会获取我们输入的长度&#xff0c;同时循环将每个字符的ASCII码与ecx进行异或运算&#xff0c;最后与“VeiajeEjbavwij”进行对比
那么ecx是谁呢&#xff0c;我们通过x32dbg可以看出为字符串“2000"循环&#xff0c;每次读取一位&#xff0c;循环读取&#xff0c;同030号程序一样
那么下面的异或4是哪里来的呢&#xff0c;我们可以看到00402D02处把4压栈
以下是PASSWORD计算代码
00402C5F | 0F8F EF000000 | jg cracking4all.2.402D54 |
00402C65 | 0FBFD0 | movsx edx,ax |
00402C68 | 8D4D 98 | lea ecx,dword ptr ss:[ebp-68] |
00402C6B | 8D45 D8 | lea eax,dword ptr ss:[ebp-28] |
00402C6E | 51 | push ecx |
00402C6F | 52 | push edx |
00402C70 | 8D4D 88 | lea ecx,dword ptr ss:[ebp-78] |
00402C73 | 50 | push eax |
00402C74 | 51 | push ecx |
00402C75 | C745 A0 01000000 | mov dword ptr ss:[ebp-60],1 |
00402C7C | C745 98 02000000 | mov dword ptr ss:[ebp-68],2 |
00402C83 | FFD3 | call ebx |
00402C85 | 8D95 78FFFFFF | lea edx,dword ptr ss:[ebp-88] |
00402C8B | 6A 01 | push 1 |
00402C8D | 8D85 68FFFFFF | lea eax,dword ptr ss:[ebp-98] |
00402C93 | 52 | push edx |
00402C94 | 50 | push eax |
00402C95 | C745 80 04000000 | mov dword ptr ss:[ebp-80],4 |
00402C9C | C785 78FFFFFF 02000000 | mov dword ptr ss:[ebp-88],2 |
00402CA6 | FF15 AC614000 | call dword ptr ds:[<&rtcLeftCharVar>] |
00402CAC | 8D8D 68FFFFFF | lea ecx,dword ptr ss:[ebp-98] |
00402CB2 | 8D55 AC | lea edx,dword ptr ss:[ebp-54] |
00402CB5 | 51 | push ecx |
00402CB6 | 52 | push edx |
00402CB7 | FFD7 | call edi |
00402CB9 | 50 | push eax |
00402CBA | FFD6 | call esi |
00402CBC | 0FBFD8 | movsx ebx,ax |
00402CBF | 8D45 88 | lea eax,dword ptr ss:[ebp-78] |
00402CC2 | 8D4D B0 | lea ecx,dword ptr ss:[ebp-50] |
00402CC5 | 50 | push eax |
00402CC6 | 51 | push ecx |
00402CC7 | FFD7 | call edi |
00402CC9 | 50 | push eax |
00402CCA | FFD6 | call esi |
00402CCC | 0FBFD0 | movsx edx,ax |
00402CCF | 33DA | xor ebx,edx |
00402CD1 | 8D85 58FFFFFF | lea eax,dword ptr ss:[ebp-A8] |
00402CD7 | 53 | push ebx |
00402CD8 | 50 | push eax |
00402CD9 | FF15 6C614000 | call dword ptr ds:[<&rtcVarBstrFromAnsi |
00402CDF | 8D4D C8 | lea ecx,dword ptr ss:[ebp-38] |
00402CE2 | 8D95 58FFFFFF | lea edx,dword ptr ss:[ebp-A8] |
00402CE8 | 51 | push ecx |
00402CE9 | 8D85 48FFFFFF | lea eax,dword ptr ss:[ebp-B8] |
00402CEF | 52 | push edx |
00402CF0 | 50 | push eax |
00402CF1 | FF15 78614000 | call dword ptr ds:[<&__vbaVarCat>] |
00402CF7 | 8BD0 | mov edx,eax |
00402CF9 | 8D4D C8 | lea ecx,dword ptr ss:[ebp-38] |
00402CFC | FF15 00614000 | call dword ptr ds:[<&__vbaVarMove>] |
00402D02 | 8D4D AC | lea ecx,dword ptr ss:[ebp-54] |
00402D05 | 8D55 B0 | lea edx,dword ptr ss:[ebp-50] |
00402D08 | 51 | push ecx |
00402D09 | 52 | push edx |
00402D0A | 6A 02 | push 2 |
00402D0C | FF15 94614000 | call dword ptr ds:[<&__vbaFreeStrList>] |
00402D12 | 83C4 0C | add esp,C |
00402D15 | 8D85 58FFFFFF | lea eax,dword ptr ss:[ebp-A8] |
00402D1B | 8D8D 68FFFFFF | lea ecx,dword ptr ss:[ebp-98] |
00402D21 | 8D95 78FFFFFF | lea edx,dword ptr ss:[ebp-88] |
00402D27 | 50 | push eax |
00402D28 | 51 | push ecx |
00402D29 | 8D45 88 | lea eax,dword ptr ss:[ebp-78] |
00402D2C | 52 | push edx |
00402D2D | 8D4D 98 | lea ecx,dword ptr ss:[ebp-68] |
00402D30 | 50 | push eax |
00402D31 | 51 | push ecx |
00402D32 | 6A 05 | push 5 |
00402D34 | FF15 08614000 | call dword ptr ds:[<&__vbaFreeVarList>] |
00402D3A | B8 01000000 | mov eax,1 |
00402D3F | 83C4 18 | add esp,18 |
00402D42 | 66:0345 C4 | add ax,word ptr ss:[ebp-3C] |
00402D46 | 0F80 A0030000 | jo cracking4all.2.4030EC |
00402D4C | 8945 C4 | mov dword ptr ss:[ebp-3C],eax |
00402D4F | E9 FEFEFFFF | jmp cracking4all.2.402C52 |
Python代码
dst_pwd &#61; &#39;VeiajeEjbavwij&#39;
src_pwd &#61; &#39;&#39;
for k, v in enumerate(dst_pwd):src_pwd &#61; src_pwd &#43; chr((ord(v) ^ ord(&#39;2000&#39;[k % 4])) ^ ord(&#39;4&#39;))
print(src_pwd)
结果为“PamelaAnderson”&#xff0c;带入到程序内





 京公网安备 11010802041100号
京公网安备 11010802041100号